700 Million LinkedIn Users' Data Sold on Dark Web Forum
Hacker TomLiner posted personal information from nearly all LinkedIn members in June 2021, sparking debate over data scraping versus breach classification
Sagsdetaljer
Quick Facts
Quick Facts
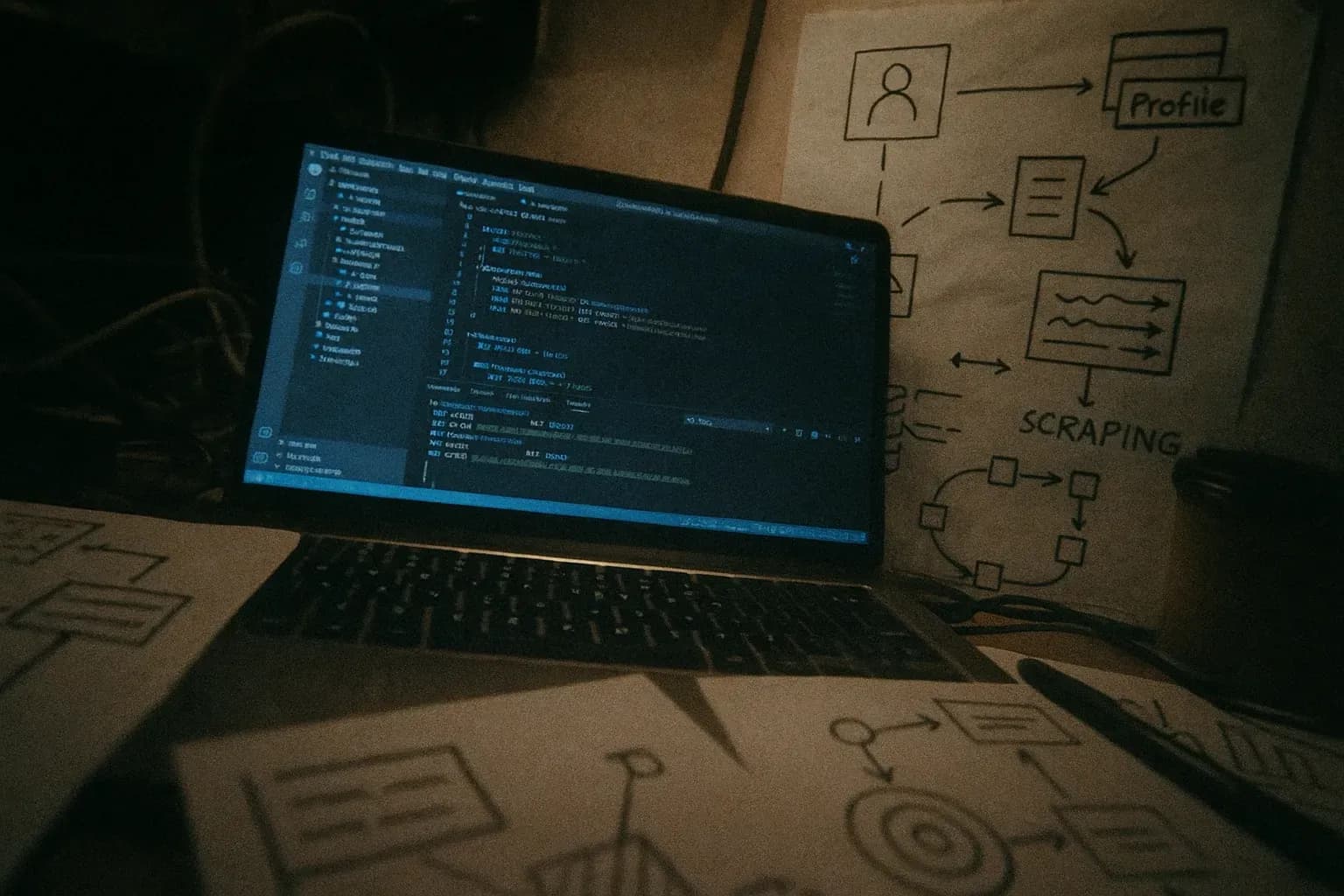
On June 22, 2021, a hacker operating under the username TomLiner posted a claim on RaidForums—a notorious dark web marketplace—that they possessed personal information on 700 million LinkedIn users. The seller advertised the dataset for approximately $5,000 and provided a sample of 1 million records as proof of authenticity.
Security researchers quickly verified the sample data. Multiple outlets including Privacy Sharks, RestorePrivacy, and Hackread.com confirmed the records were genuine and current, containing information harvested between 2020 and 2021. At the time of the incident, LinkedIn had approximately 756 million members, meaning the exposed dataset covered roughly 92-93% of the platform's entire user base.
The data exposed in the compilation included extensive personal and professional details: full names, email addresses, phone numbers, physical addresses, geolocation information, LinkedIn usernames and profile URLs, gender, work history, industry classifications, and inferred salary data. Researchers also found references to other social media accounts and usernames associated with individuals in the dataset.
LinkedIn's response centered on a critical distinction. The company, speaking through spokespeople including Leonna Spilman, stated this was not a data breach in the traditional sense. Instead, LinkedIn characterized the incident as unauthorized scraping of publicly visible profile information combined with data aggregated from other sources. Critically, the company confirmed that no private member data or passwords were compromised. LinkedIn emphasized that the scraping violated its Terms of Service and that the company actively works to prevent such activities.
This incident was not the first of its kind. Four months earlier, in April 2021, another threat actor had offered data from 500 million LinkedIn users using the same scraping methodology. The recurring nature of these incidents highlighted vulnerabilities in how public profile data could be harvested at scale.


