Espionage
The hidden battle for state secrets, double lives, and treason
What is espionage, really? Delve into a world of secret agents, cyber warfare, and treason, where national security and human lives are at stake.
The hidden battle for state secrets, double lives, and treason
Espionage: Covert gathering to the threat of treason
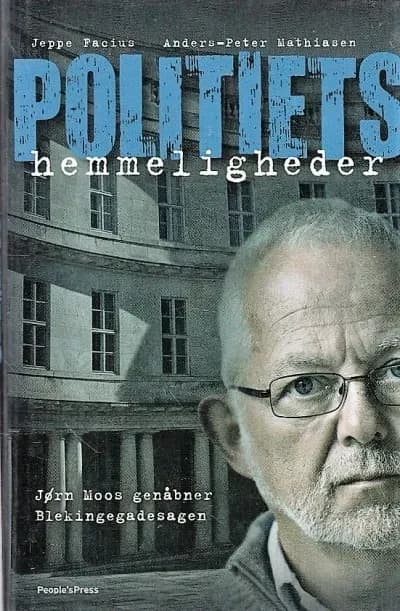
Within the true crime universe, espionage covers the secret and often illegal acquisition of confidential information or state secrets, typically for the benefit of a foreign power, a hostile organization, or a competing individual. This serious form of crime, often carried out by or directed against intelligence services, opens a door to a world of hidden agendas and potentially devastating treason. Espionage cases are characterized by their complex planning, the possible double lives of those involved as double agents, and the far-reaching consequences that can threaten national security, economic stability, or personal freedoms.
Infiltration to cyberattacks: How spies operate and why
Perpetrators of espionage, often referred to as spies, employ a wide range of methods. These range from classic human intelligence (HUMINT), where agents are recruited and infiltrate targets, to sophisticated cybercrime and cyber-espionage aimed at stealing digital information and disrupting systems. The motivations behind espionage are equally varied and can include ideological conviction, financial gain – for example, through industrial espionage – blackmail, or personal revenge. This creates deeply complex human dramas where loyalty and morality are constantly challenged. Often, these criminal activities unfold in the shadows, far from the public eye, until a revelation brings the intricate networks and serious breaches of trust to light.
Eternal battle: How CIA/KGB spies challenge investigators
For investigators and authorities involved in counter-espionage, espionage cases present a formidable challenge. They often involve sophisticated state actors or organizations, such as notorious intelligence agencies like the CIA or the former KGB, which use encrypted communication and operate across national borders, complicating international cooperation. Solving these cases can take years and requires a profound understanding of both advanced technological tools and complex human psychology. Exposed espionage cases, whether occurring in peacetime or in the lead-up to war, illustrate not only the extensive damage caused by leaked secrets but also the constant battle between information protection and information gathering. This makes espionage an eternally relevant and often frightening phenomenon in the true crime landscape, balancing on the edge between state security interests and individual criminal acts.
Threat of espionage: Geopolitical tensions to cyber war
Espionage is thus more than just a crime; it is a reflection of geopolitical tensions, international power struggles, and human vulnerability, where the lines between national interest, intelligence activities, and criminal acts are often blurred. The continued existence and evolution of espionage, especially in an increasingly digitized world characterized by cyber threats and potential information warfare, underscore the ongoing need for vigilance, robust national security, and advanced investigative methods to counter this hidden threat, which affects society at all levels.
Fascinated by the shadow world of espionage? Explore cases of treason and high-tech information warfare. Delve into real-life espionage cases – find our exciting cases below.